Rust Articles & Tutorials
Deep-dive articles on every corner of Rust — from ownership fundamentals to post-quantum cryptography. Written for engineers who want to understand the why, not just the how.
118+
Articles
16
Topics
All Free
No paywall
Collections & Data Structures(6)
Choosing the Right Collection Type in Rust
Rust provides several data types in its Standard Library to allow users to store multiple values of the same type together. Three primary…
Mastering Pattern Matching in Rust
In Rust, one of the core features that distinguishes it from many other languages is its powerful system for pattern matching. Pattern…
Understanding VecDeque, LinkedList, and BinaryHeap in Rust
Hey there! If you’ve dabbled in programming, you know that picking the right data structure can make a world of difference.
Building a Graph Database in Rust
Unlike traditional relational databases, which represent data in tables, graph databases capture the rich relationships between entities as…
Implementing a Vector Database in Rust
Unlike traditional databases that store scalar data (like integers, strings, etc.), vector databases are designed to efficiently store and…
Understanding Partial Equivalence in Rust’s Floating-Point Types
When working with numeric types in programming, we generally assume that numbers behave in ways that are predictable and consistent. For…
Concurrency & Async(25)

Tokio: A Runtime for Writing Reliable, Asynchronous Applications with Rust
What is Tokio?
Writing Async Code in Rust
Traditional synchronous code executes step-by-step, blocking subsequent operations until the current one finishes. In I/O-bound scenarios…
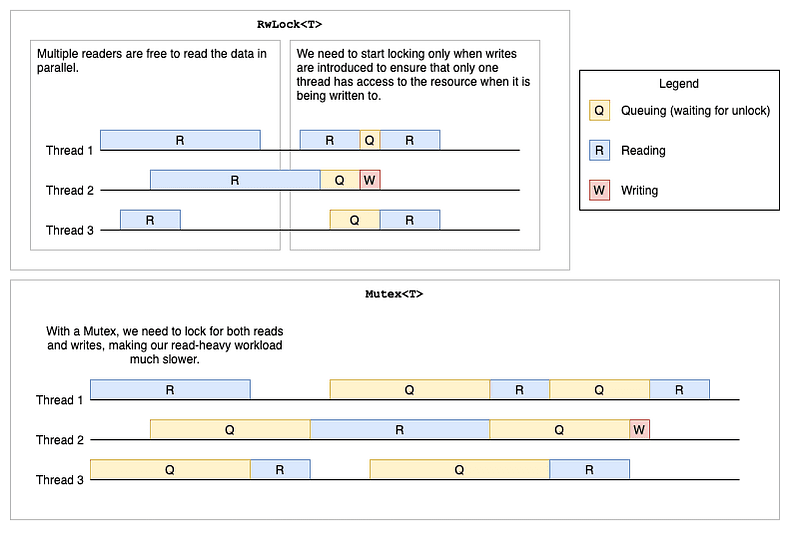
Sharing Data Between Threads in Rust
Rust is renowned for its emphasis on safety, particularly concurrent safety. One of the challenges in concurrent programming is the safe…
Secure Socket Layer (SSL/TLS) with Rust: A Primer
In this article, we will briefly introduce SSL/TLS and then delve into a working example of setting up a TLS server and client using Rust.

Crafting a Secure Server-to-Server Handshake with Rust & OpenSSL
Hello there, fellow tech enthusiast! 🦀
Building a Function-as-a-Service (FaaS) in Rust
Welcome to this tutorial on building a Function as a Service (FaaS) system using Rust.
Implementing a VPN Server in Rust
Interested in understanding the inner workings of a VPN? Thinking about setting up your own VPN server? Today, we’re taking a…
Building an Event Broker in Rust
In this step-by-step guide, we're diving into the exciting world of building a simple event broker using Rust.
Asynchronous Design Patterns in Rust
Hey there, Rustacean! 🦀
Using Channels in Rust: Why and When?
Hey there! If you’re diving into the world of concurrent programming with Rust, you’ve probably come across the term “channels”. But what…
Working with Asynchronous Streams in Rust
Asynchronous programming can be a bit challenging to grasp, but it’s incredibly useful for improving the performance of programs that deal…
Implementing a DNS Server in Rust
The Domain Name System (DNS) is a foundational aspect of the internet, translating human-readable domain names into IP addresses that…
3 Popular Crates for Working with Containers in Rust
Hey there, Rustaceans! 🦀 Let’s talk containers.
Rust Crates for Working with LLM
In this article, we’ll look at five Rust crates, each offering tools to easily integrate these advanced models into your Rust projects…

Handling multiple asynchronous operations easily with Rust ‘select!’
The select! macro is designed to manage multiple asynchronous operations, allowing a program to wait on several tasks simultaneously and…
Linux Network Namespaces in Rust
Linux Network Namespaces are a feature within the Linux kernel that allows for the isolation and virtualization of network resources. This…
WebAssembly in Rust
Hello, fellow Rustaceans! 🦀
Rust Concurrency in Practice
Concurrency in Rust is based on ownership, types, and borrowing principles, which help manage memory safety without a garbage collector.
Thread Boundaries in Rust
Hi, fellow Rustaceans! 🦀
Raft Cluster in Rust
In today’s article, we will explore how to implement a basic Raft-based consensus system in Rust. 🦀
Implementing a Distributed State Machine in Rust
In this guide, we’ll walk through the creation of a simplified distributed state machine using Rust. 🦀
Low Latency in Rust with Lock-Free Data Structures
In high-performance and distributed systems, latency is a factor that affects overall system responsiveness and throughput. Traditional…
Data-Parallelism in Rust with the Rayon Crate
The Rayon crate is one of the most popular libraries for data-parallelism in Rust , providing a simple and efficient way to execute…
Rust: From Simple Functions to Advanced Abstractions
While many tutorials introduce isolated features, this article takes a holistic, practical approach: we’ll start with a simple example and…
Atomics in Rust: Lock-Free Does Not Mean Free
Atomics are lock-free because they execute entirely in hardware. An atomic read-modify-write is performed by the CPU using instructions…
Cryptography & Blockchain(11)
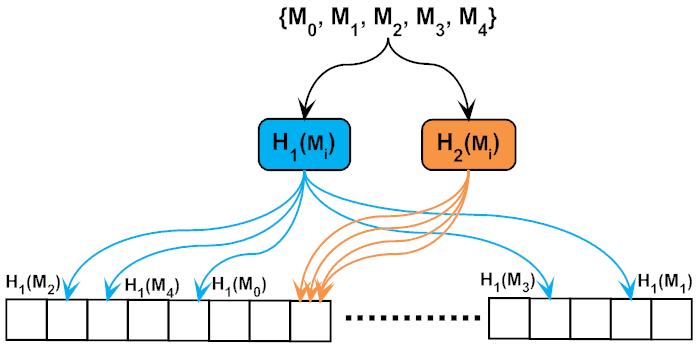
Exploring Hash functions in Rust: Fowler–Noll–Vo (FNV), SipHash, and beyond
Hash functions are fundamental in numerous computing scenarios, offering ways to represent arbitrary-sized data in fixed-sized values. In…
Implementing zk-SNARK Zero Knowledge Proof in Rust
Imagine holding a sealed envelope containing a secret message. You’re tasked with proving the message’s contents to a friend, but here’s…
Rusting Up Your Own Self-Signed Certificate Generator
If you’ve dipped your toes in the sea of server administration or web development, you’ve likely come across SSL/TLS certificates. They’re…
What is the Noise Protocol
Introduction to the Noise Protocol Framework
Implementing Zero Knowledge Multi-Party Computation in Rust
In this tutorial, we explore the foundational concepts and practical implementation of a simplified zk-rollup-like system in Rust! 🦀
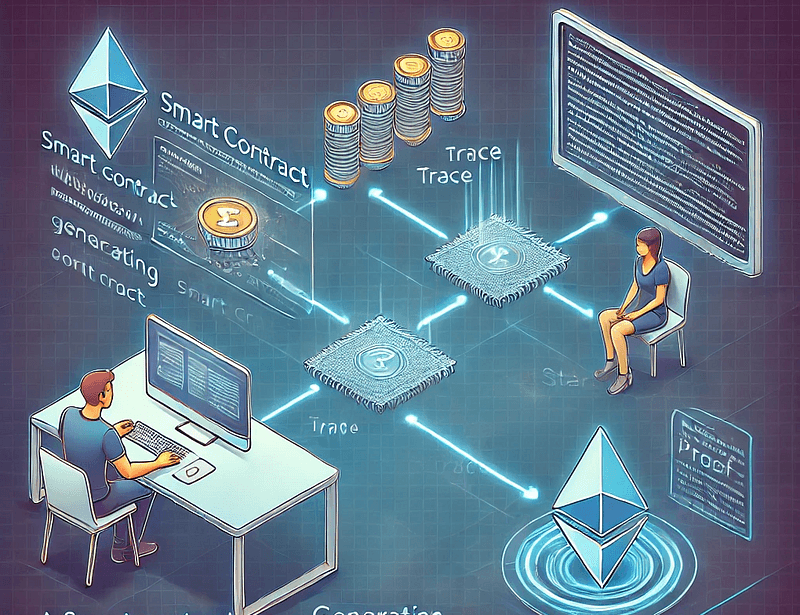
Introduction to Provable Smart Contracts
Provable smart contracts use cryptographic techniques to verify that computations done outside the blockchain are correct. This means that…
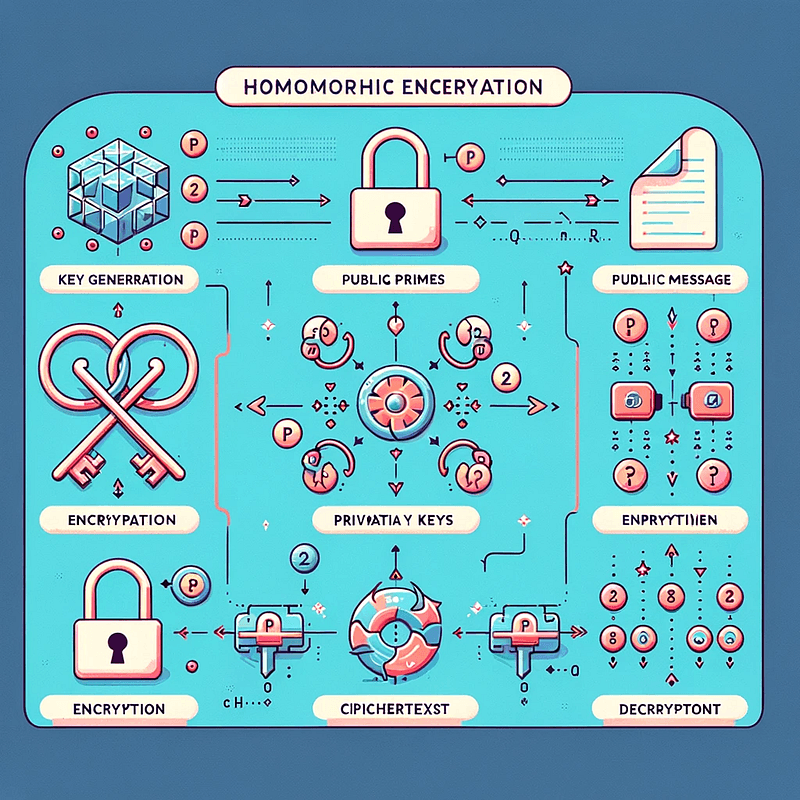
Homomorphic Encryption in Rust: Developing Secure Data Analysis
Homomorphic encryption allows computations to be performed on encrypted data without decrypting it first. This property is particularly…
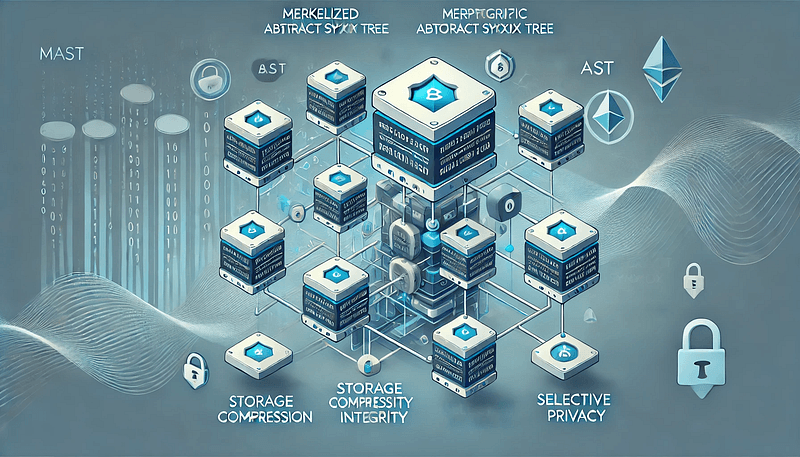
Optimizing Blockchain with Merkelized Abstract Syntax Trees in Rust
The increasing size of blockchain data is a significant challenge for Blockchain performance, data integrity, and privacy. Merkelized…
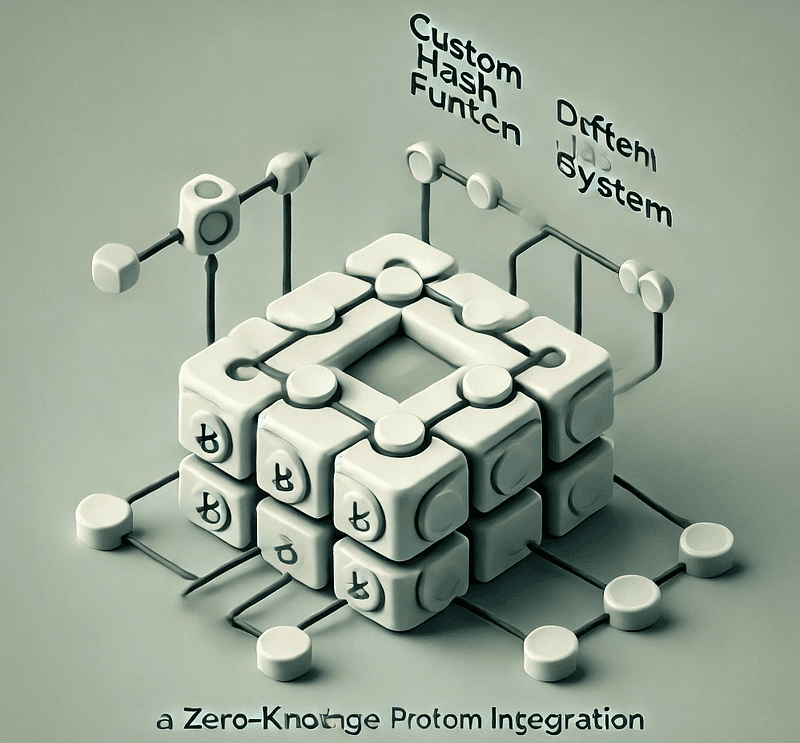
Building a ZKP system from scratch in Rust
New to zero-knowledge proofs? This is part of my ZK Proof First Steps series, where we’re building a ZKP system from scratch in Rust! 🚀
Building a Threshold Cryptography Library in Rust
Threshold cryptography allows secure splitting of a secret into multiple pieces, called “shares.”
Your Stack Is Leaking: How Memory Operations Expose Cryptographic Secrets in Rust
Learn how Rust's stack and heap retain sensitive cryptographic key material after drop, how attackers exploit residual memory through cold boot attacks, crash dumps, and timing oracles — and how to prevent it using zeroize, secrecy, and constant-time comparisons.
Error Handling(2)
Iterators & Closures(6)
Iterator Chains in Rust: Power, Elegance, and Zero-Cost Abstraction
A deep dive into Rust's iterator system — what it is, how the compiler thinks about it, and how to wield it effectively for composable, zero-cost data transformations.

What are closures in Rust?
What Are Closures?
The Rust Closure Cookbook: Patterns, Tips, and Best Practices
Imagine you’re crafting a neat piece of code, and you’ve got a chunk of logic you want to pass around like a hot potato. That’s where…
Functional Programming Patterns in Rust
Hey there!
Combinators in Rust
Combinators are higher-order functions that can combine or transform functions, enabling more abstract and concise code.
Field-Programmable Gate Arrays (FPGAs) Simulator in Rust
Field-Programmable Gate Arrays (FPGAs) are integrated circuits designed to be configured by a customer or a designer after manufacturing…
Lifetimes(3)
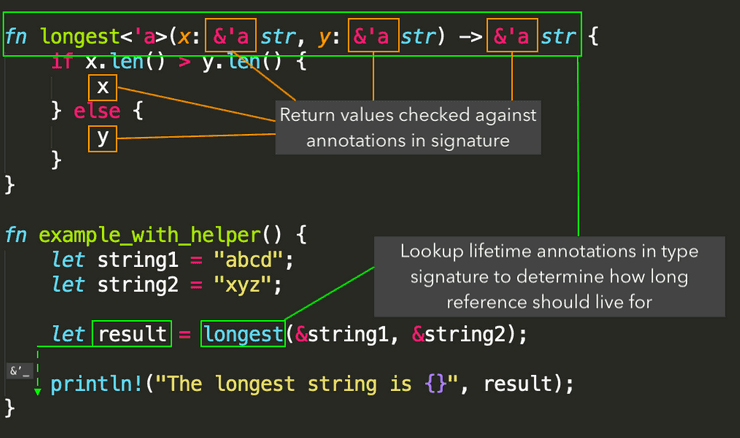
Diving Deep: How Rust Lifetimes Work
In Rust, lifetimes are denoted using a single quote, like 'a, indicating how long a reference to data should be valid. It's a mechanism…
Referencing, Deep Cloning, and Shallow Cloning in Rust
Hi, fellow Rustaceans!

Rust Lifetimes Made Simple
🦀 Rust lifetimes are one of the language’s most powerful and intimidating features. They exist to ensure that references are valid for as…
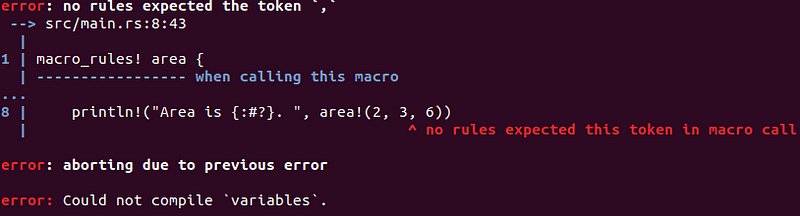
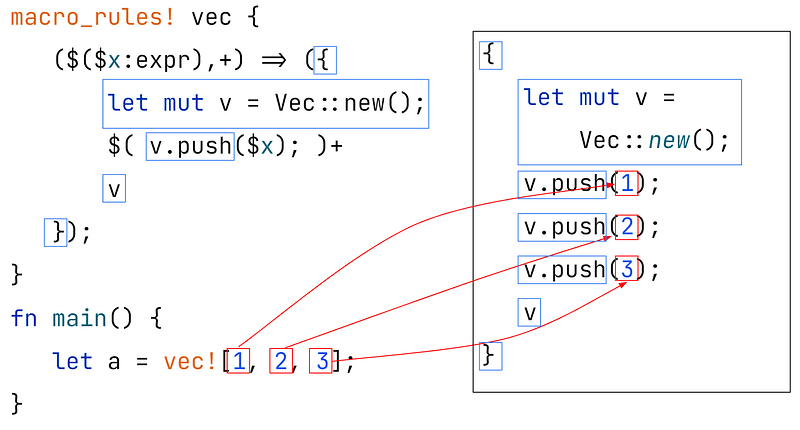
Macros(3)
Exploring Rust Attributes in Depth
What are Attributes in Rust?
Dynamic Code Generation in Rust
Hi there, fellow Rustaceans! 🦀
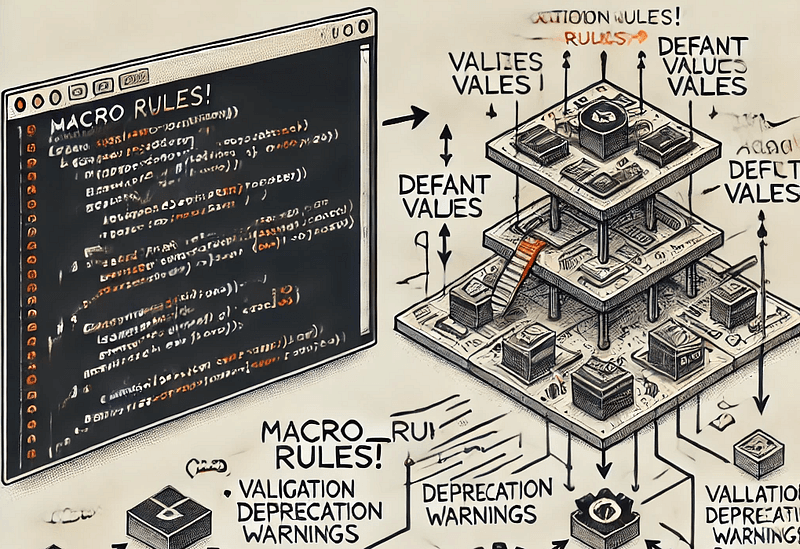
Creating flexible, complex, and reusable structures in Rust with macros
Macros in Rust are a convenient and powerful way to write code that writes other code, enabling you to create highly reusable and flexible…
Ownership & Borrowing(3)

How Memory Safety works in Rust
Memory safety refers to ensuring that a program’s memory access is valid and does not cause unexpected behaviour such as crashes or…
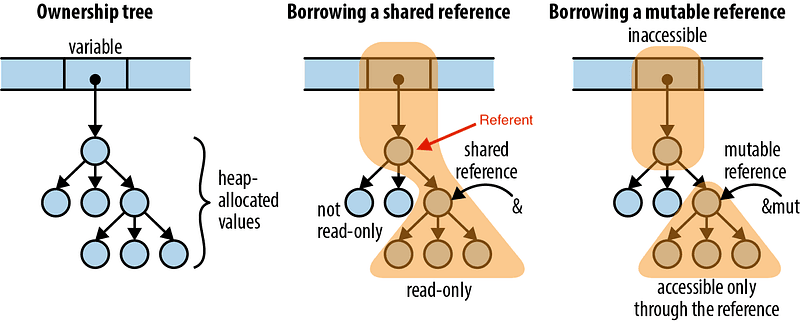
Understanding Ownership in Rust with Examples
The Rust programming language offers a unique approach to memory management, combining aspects of both automatic and manual memory…
Mutable vs Immutable Borrowing in Rust
Borrowing, in its mutable and immutable forms, is a cornerstone of Rust’s promise for memory safety without a garbage collector. While it…
Patterns & Architecture(1)
Performance & Optimization(4)
Rust Compile Time Optimization: Making Your Builds Lightning Fast
Learn proven techniques to dramatically reduce Rust compile times. From incremental compilation to workspace optimization and caching strategies.
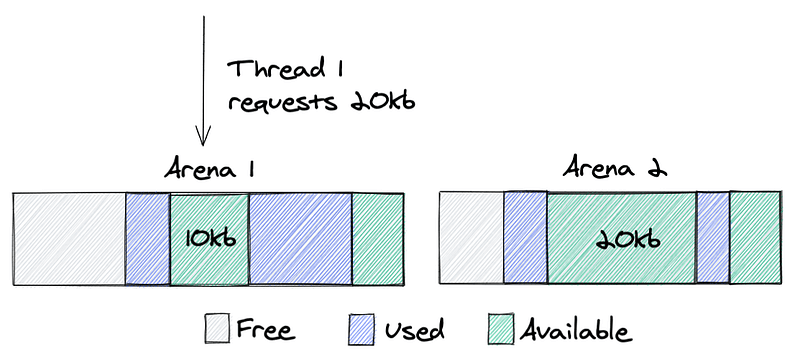
Rust under the hood: the jemalloc Memory Allocation algorithm
Introduction to jemalloc
Rust Performance Design Patterns: Writing Efficient and Safe Code
Hey there! Are you dipping your toes into the Rusty waters of system-level programming? Or maybe you’re already sailing along the Rustacean…
Rust Byte Alignment Basics
Byte alignment, also known as data alignment, refers to arranging the memory addresses of data structures so that they align with certain…
Smart Pointers & Memory(5)

Boxing and Unboxing in Rust
Boxing in Rust refers to the process of allocating data on the heap and storing a reference to it on the stack. This is achieved using the…
Smart Pointers in Rust
Rust introduces smart pointers as a powerful feature for memory management. Unlike traditional pointers in languages like C++, Rust’s smart…
Rust Structs and Enums Under the Hood
Understanding a bit about the inner mechanics and how structs and enums behave regarding memory allocation and performance provides deep…
A Simple Cache System in Rust
In this article, we will see how to build a basic yet efficient Least Recently Used (LRU) cache system in Rust, complete with an eviction…
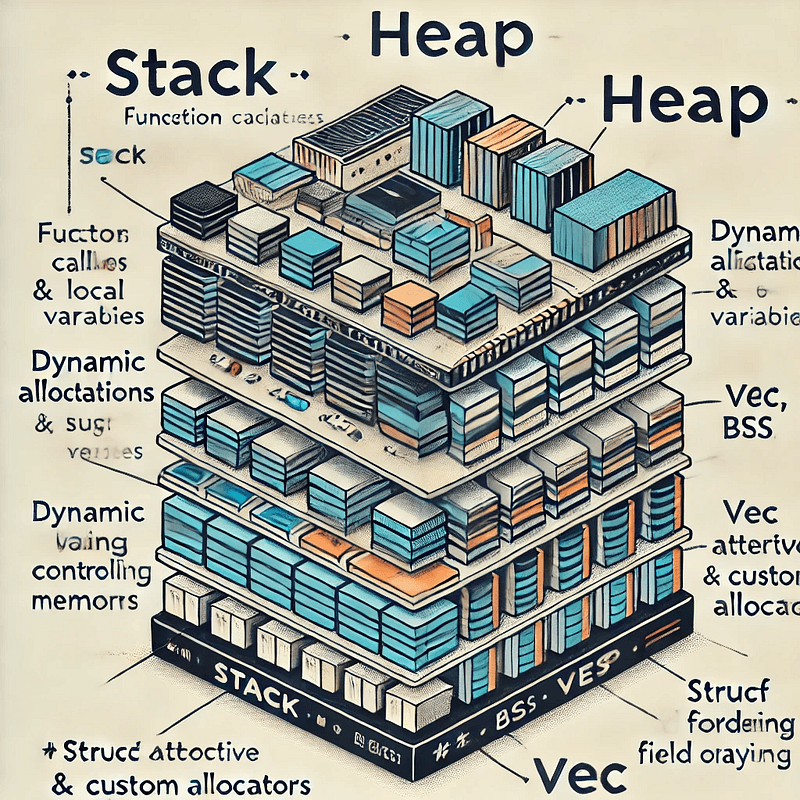
Rust Memory Layouts in Practice
Memory layout refers to how data is organized in memory, which affects performance, safety, and interoperability with other languages and…
Strings & Text(18)
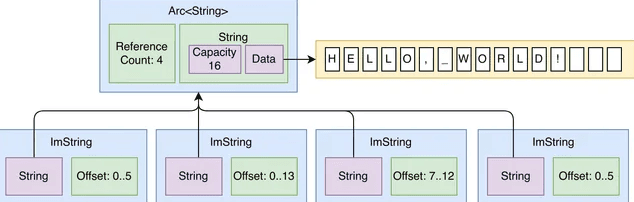
Working with Strings in Rust: A Definitive Guide
Rust’s approach to strings can be a bit challenging for newcomers to the language or developers familiar with strings in other languages…
Data Serialization in Rust with Serde
In our digital age, data is the lifeblood of countless applications. But there’s a tiny secret behind the scenes: the art and science of…
Implementing a Secret Vault in Rust
Hey there, fellow Rustacean!
Building a P2P Database in Rust
Hey there! If you’ve landed here, you’re probably interested in understanding how distributed systems work, particularly in Rust. Today…
Understanding String, str, and UTF-8 byte arrays in Rust
Hey there! Ever wonder how we’ve managed to squeeze every language from the intricate scripts of Mandarin to the hieroglyphs of ancient…
Understanding and Implementing OAuth 2.0 in Rust with oxide-auth
Overview of the OAuth 2.0 Protocol
Implementing a Firewall in Rust
In this article, we will implement a basic yet fully functional Firewall in Rust! 🦀
Implementing a Blockchain in Rust
This article provides a step-by-step breakdown of implementing a basic blockchain in Rust, from the initial setup of the block structure…
Building a VM Instruction Set in Rust
In this comprehensive tutorial, we’ll build a basic Virtual Machine (VM) in Rust. It isn’t just about coding; it’s about understanding the…

Rust Parsing with Pest and Pest Derive Crates
Pest is a parsing library in Rust that emphasizes simplicity and performance. It uses Parsing Expression Grammar (PEG) as its foundation…
Database Sharding in Rust
Database sharding is a technique to scale out databases by breaking them into smaller, more manageable pieces called shards. It’s…
Implementing a Virtual DOM in Rust
In this article, we explore the implementation of a basic virtual DOM for parsing and rendering HTML elements using Rust.
Implementing a Web3 NFT API in Rust
Hi fellow Rustaceans! 🦀
Implementing an Arithmetic Circuit Compiler in Rust
Implementing an arithmetic circuit compiler in Rust involves creating a system that can parse a polynomial expression, construct an…
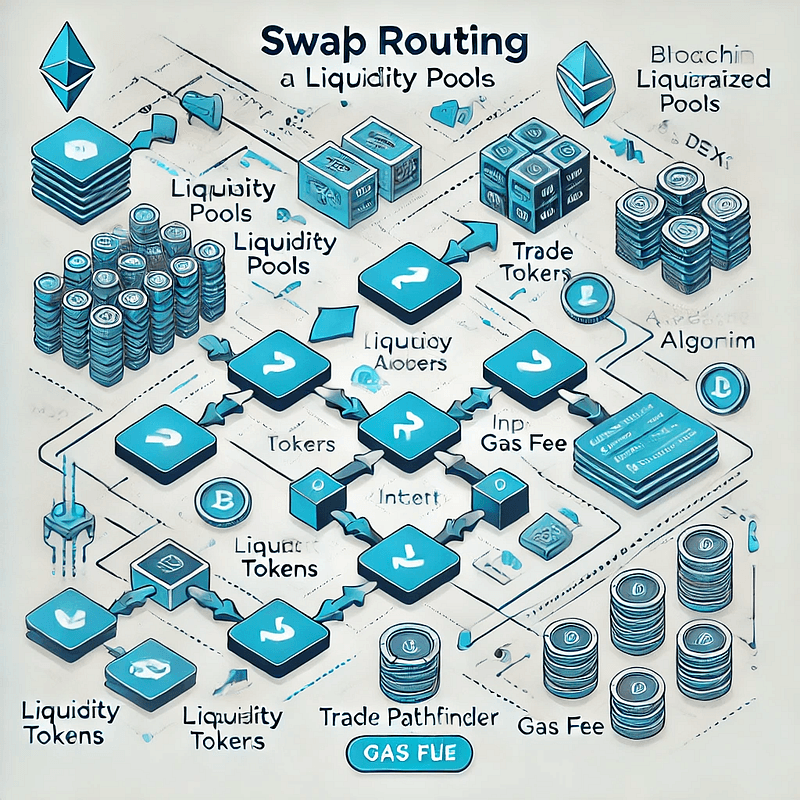
Implementing a Swap Routing Mechanism in Rust
In this article, we’ll explore how to implement a swap routing mechanism in Rust. We’ll create a simplified version of a decentralized…
A Memory Dump Analyzer in Rust
Analyzing binary files and memory dumps is a common task in software development, especially in cybersecurity, reverse engineering, and…
Mastering Pinning in Rust
Pinning in Rust is an essential concept for scenarios where certain values in memory must remain in a fixed location, making it critical…
Building a VM with Native ZK Proof Generation in Rust
In this article we will build a cryptographic virtual machine (VM) in Rust, inspired by the TinyRAM model, using a reduced instruction set…
Systems Programming(9)
Rust Embedded Programming: Building Firmware from Scratch
Master embedded Rust development. Build real-world firmware with no_std, embedded-hal, and hardware abstraction for microcontrollers.
Implementing a Network Traffic Analyzer in Rust
In this article, we’ll delve into the intricacies of working with network traffic using Rust. We’ll explore capturing packets, parsing…
Implementing an Application Container in Rust
Hey there, Rustaceans! 🦀
Memory-Mapped I/O in Rust
Memory-mapped I/O is especially helpful when working with big files, loading only the necessary parts into memory. This makes it simpler to…
Exploring Finite Fields with Rust: Efficient Modular Arithmetic
Finite fields might sound like abstract mathematical concepts, but they are at the heart of many technologies we rely on today, especially…
Inline assembly in Rust
Inline assembly in Rust, specifically with the asm! macro, allows developers to insert assembly language instructions directly into Rust…
Playing with Pointer Arithmetic in Rust
In most modern languages, pointer arithmetic is an unusual sight, often left behind in favor of safety and memory management features.
Dynamic Linking and Memory Relocations in Rust
When you compile source code into object files (such as .o files), the compiler generates machine code along with metadata that indicates…
Userspace TCP in Rust with DPDK for High-Frequency Trading
Who This Article Is For — And a Warning
Testing(2)

Rust Testing Mastery: From Basics to Best Practices
This article provides a comprehensive overview of testing in Rust, delving into its built-in test framework, common patterns, useful…

Building an Error Correction System in Rust
Error correction is a key component of communication and data storage systems. Techniques like Reed-Solomon error correction ensure data…
Traits & Generics(9)
Understanding Rust's Traits: An Introduction and Examples
What Are Traits?
Mastering Generics in Rust: A Hands-on Guide
Generics allow us to define function signatures and data types with placeholder type instead of concrete types. This helps in writing more…
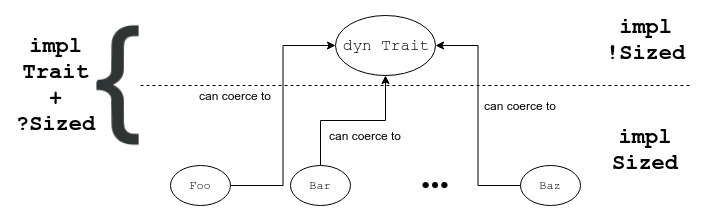
Rust Dynamic vs Static Dispatch
Dynamic and static dispatch are two different ways of handling method calls in the Rust programming language. Understanding the differences…
Understanding Rust’s Generic Associated Types
Generic Associated Types (GATs) allow for more expressive type relationships in traits, enhancing the language’s capabilities in generic…
Rust Traits: from Zero to Hero
Who’s never stumbled upon the tricky “the (…) trait bound is not satisfied” when coding in Rust? We have all been there!
Implementing a Mersenne Twister Generator in Rust
The Mersenne Twister is a widely used pseudorandom number generator (PRNG) known for its fast generation and high-quality randomness…
The Architecture of Elasticity: Escaping “Generic Soup” with Type Erasure
In the Rust ecosystem, “Zero-Cost Abstractions” is the mantra. We are culturally conditioned to view Generics (<T: Trait>) as the only…
Rust’s trait system is one of its most powerful features, enabling zero-cost abstractions and…
This article assumes familiarity with Rust traits, generics, and trait bounds. We’ll explore the pyramid pattern through three complete…
Beyond dyn Trait: Advanced Runtime Polymorphism and the Caster Pattern
In Rust, we are evangelists of static analysis. We lean on monomorphization, forcing the compiler to generate specialized assembly for…
Web & Networking(11)

What’s Zero Trust?
Zero Trust is a security concept based on assuming that all devices, users, and systems inside and outside of an organization’s network are…

An Introduction to Actix: A Rust Web Framework
Actix is a robust, pragmatic, fast Rust framework for web application building. It utilizes the actor model for managing state and…
Working with Databases in Rust using Diesel
Hey there, Rustacean! 🦀
gRPC over HTTP/2 in Rust
If you’re keen on enhancing your networked applications in Rust, you’ve come to the right place. Today, we’re exploring Tonic, Rust’s take…
Implementing a fully functional API Gateway in Rust: Part 1
Welcome to the first part of our comprehensive series dedicated to constructing a fully functional API Gateway using the Rust programming…
Mastering Unix System Calls with Rust’s Nix Crate
Ever wanted to tap into the power of Unix system calls using Rust? You’re in the right place. In this article, we’ll delve into the nix…
Implementing a Fully Functional API Gateway in Rust: Part II — Dynamic Service Registry
Hey there, Rustaceans! 🦀
Machine Learning in Rust
Hi everyone! In this article, we’re focusing on machine learning in Rust.
Six Rust Crates for Networking
Today, we’re exploring six popular Rust crates in Rust network programming. From handling low-level socket operations with Socket2 to…
Decentralized Networking with the libp2p Rust Library
Before we delve into the Rust crate, let’s understand what libp2p is and why it matters. Libp2p is a modular and extensible networking…
Building a Rust Serverless Platform
In this tutorial, we will build a WebAssembly-powered serverless platform using Rust 🦀. This platform will enable you to register and…